Auto-ISAC on Combating Cybersecurity and Data Privacy for Remarketers
Faye Francy of Auto-ISAC and Andrea Amico of Jack Cooper Logistics led a discussion on the steps that could be taken to protect personal identifiable information stored inside the vehicles sent for remarketing.
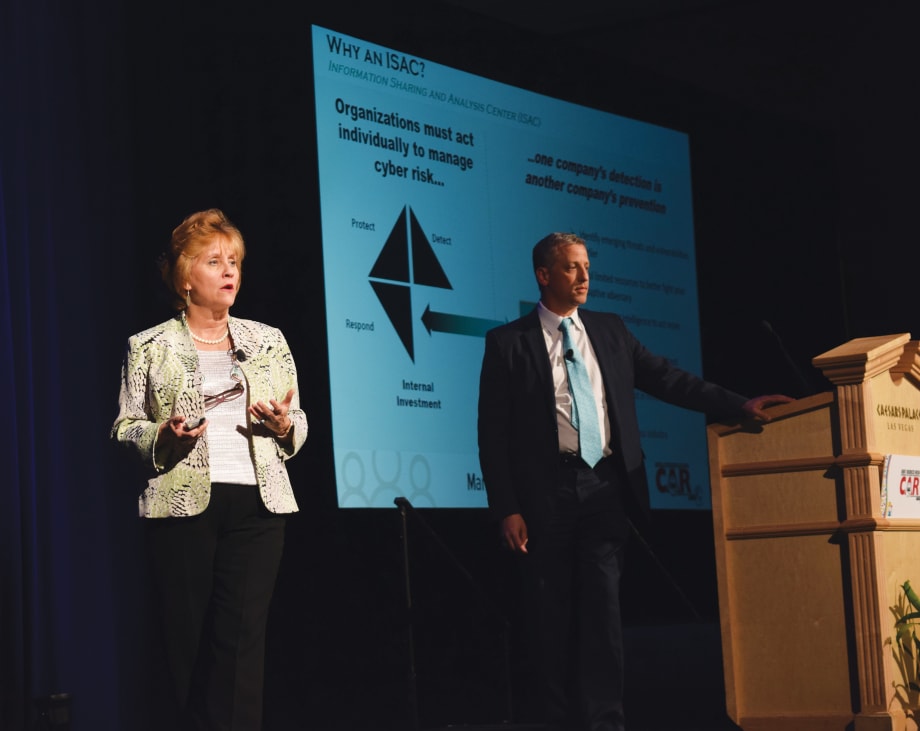
Faye Francy (left) of Auto-ISAC and Andrea Amico of Jack Cooper Logistics during the IARA townhall discussion on data privacy and cyber security threats to the remarketing industry. Photo by Andy Lundin.
Tomorrow’s remarketers will face issues surrounding vehicle technology that past remarketers never would have dreamed of.
A car knowing where you live, where you work, where your kids go to school, and where you like to have breakfast on the weekends would have been seen as a farfetched concept in the early days of the automotive industry. But, it’s a reality that we’re already living in.
As technology continues to progress, the scope of personal data stored within a vehicle will only grow, and measures will have to be put in place to keep unscrupulous hands away from it.
That’s part the Automotive Information Sharing and Analysis Center’s (Auto-ISAC) mission statement. Auto-ISAC recently partnered with the International Automotive Remarketing Alliance (IARA) for support in this goal.
At this year’s Conference of Automotive Remarketing (CAR), the IARA hosted Auto-ISAC’s executive director, Faye Francy along with Andrea Amico, president of Jack Cooper Logistics and chair of IARA’s privacy and cybersecurity initiative, for a discussion about threats to data privacy and cyber security in the remarketing industry.
“I know where people live; I know where people take their kids to school. I know their pharmacy and where their office is,” said Amico, discussing the type of information he acquired by looking at vehicle’s at various lots.
This is the type of information that vehicles currently have on their drivers, he shared. The dangerous part of this is the fact that many people don’t realize just how much data a car may have on them.
In fact, the IARA conducted a study last year in collaboration with various auctions in the U.S. and Canada that looked at 400 cars, covering 12 manufacturers and 32 makes. In this study,the organization found that more than half of the vehicles had personal information in them. It’s through this transitional period in vehicle technology, where people are still learning the extent of data that a vehicle collects, that the industry needs to find ways to safeguard personal information so cars being sent to auction aren’t full of personal data, Amico noted.
Finding Ways to Bolster Data Privacy
Amico noted a few steps that vehicle manufacturers could take to aid in this transitional period.
One step that manufacturers could take would be a rework of the current vehicle dashboard, in order to simplify the process of clearing a vehicle’s personal data.
A typical dashboard inside a vehicle today has anywhere between 30-60 buttons, he noted.
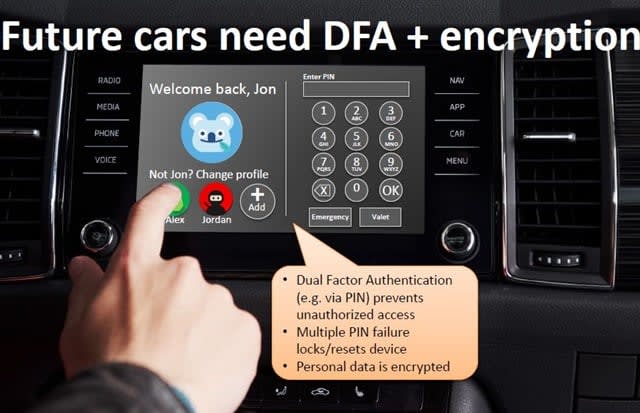
One solution brought forth to aid data privacy was the implementation of profiles within vehicle dashboards. In order for a user to log into the vehicle, they would need to enter a PIN. DFA is in reference to Dual Factor Authentication
This means that if an individual wants to attempt to clear the data on his or her vehicle, he or she would need to maneuver through all of these buttons to find the way to clear his or her data. The goal of a dashboard’s design should be to make it simple for a person to accomplish a task, not the opposite, he added.
He said the design that manufacturers should mimic the design philosophy of an iPhone. It only has four buttons, so its simple to operate, and one of those button’s primary function is to lock the device, a function that has been missing in vehicles.
If OEMs simplified their vehicle dashboards and incorporated more functions to secure the vehicle, the hurdle of clearing personal data on a vehicle would become that much easier to overcome for consumers.
Privacy-by-design should be built into future cars, but the industry doesn’t have to wait for the car of the future to start tackling this issue. That’s why IARA started the Privacy and Cybersecurity group, Amico noted.
“I don’t think anybody in this room should ever be worried about having to delete information,” Amico shared to a room of remarketing professionals at CAR.
Amico noted that Francy has been able to get him in touch with some of the people designing vehicle dashboards at various OEMS.
Another step that manufacturers could take to safeguard vehicle data would be instituting dual factor authentication, Amico added. By implementing dual factor authentication, a person would be required to enter a PIN in order to essentially log in to their vehicle. If an unauthorized user failed to enter the correct PIN multiple times, the system would lock and personal data could be reset.
In order to accommodate vehicles with multiple drivers, such as a family car or a fleet vehicle, a profile system, similar to the one you find on Netflix, could also be added to vehicles, Amico noted.
Drivers would have their own profile, as well as their own separate PIN in order to log into their respective profile. This would prevent unauthorized access to an individual’s data, since each person’s data would only be accessible by their respective profile, Amico added.
Lastly, Amico stressed that all vehicle data should be encrypted and not easily accessed.
Collaboration through Auto-ISAC
There is plenty of work still ahead in order to make vehicle data as safe as it can be. But, Auto-ISAC, along with the private companies, industry organizations, and government agencies that it partners with, are continuously working to reach that goal.
Through partnerships with industry associations like the IARA and NAFA, the knowledge base of Auto-ISAC will continue to grow, making that goal more attainable.
However, not everyone in attendance was familiar with what an ISAC was or how they came to be. Francy took some time to explain the centers’ origin.
The model for an ISAC (Information Sharing and Analysis Center) originated in 1998 under President Bill Clinton after he recognized that 80% of the critical infrastructure in the United States was owned or operated by the private sector, Francy explained.
He had concern that the private sector did not have the same intelligence that the government did, so he wanted to help. This resulted in the ISAC model, which would give the private sector the ability to collaborate amongst themselves, but also with government agencies for additional data.
The first ISAC that stood out was Financial Services ISAC, Francy noted. Today, there are roughly 23 ISACs in various fields such as IT, communications, and manufacturing.
“What we do is help to build the resiliency and see what’s happening not only amongst the company, but across the sector,” said Francy. “The mission of the ISAC is really to be the independent broker of information to help each other understand what it is, and to really share data, threat intelligence, and mitigation techniques, if, in fact, there is a bad guy out there attacking our industry.”
As a partner with the IARA, Auto-ISAC will be working with the organization to share information and figure out how they can work together to help each other, and most importantly, the industry.
More Remarketing
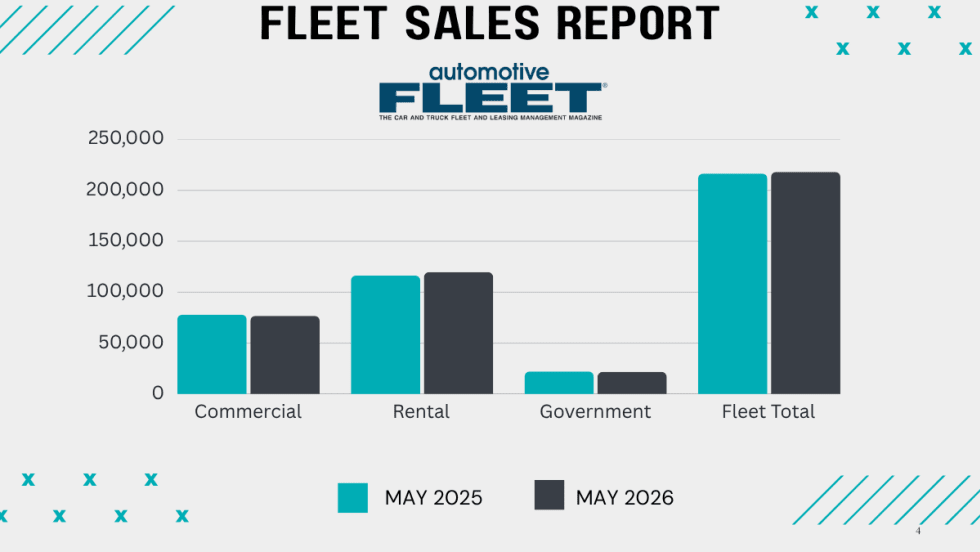
Commercial Fleet Sales Still Lead Sectors Despite May Mini Dip
The U.S. economy's continued growth and positive business investment are creating a favorable environment for fleet vehicle demand.
Read More →
How Connected Vehicle Data Is Lifting Fleet Resale Values
A vehicle health score could improve the value of fleet vehicles at remarketing. The path to a universal standard is forming, and fleets that understand the process early will be better positioned when it arrives.
Read More →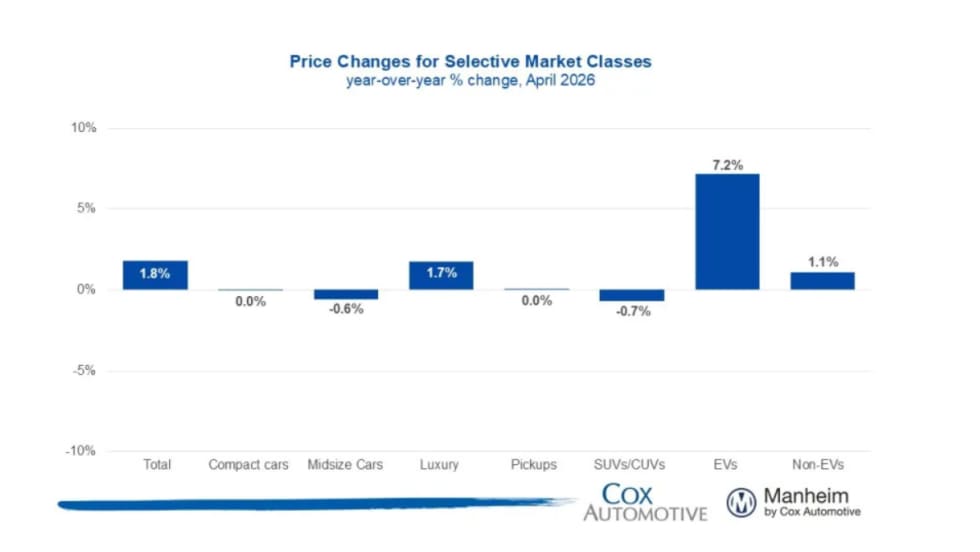
Wholesale Used Vehicle Prices Slightly Up In April
The Iranian conflict and rising gas prices inject much uncertainty into the future wholesale used vehicle markets, as higher gas prices soak up spendable income from vehicle buyers.
Read More →
CAR2026: James McKinley Wins Value Champion of the Year
James McKinley of City Rent a Truck was named the inaugural Fleet Value Champion at the CAR Conference for his data-driven approach to fleet lifecycle management and vehicle remarketing.
Read More →
CAR2026: Eric Autenrieth Wins Remarketer of the Year
Eric Autenrieth was recognized at this year's CAR Conference as the Remarketer of the Year.
Read More →
CAR2026: Lawrence Knapp Wins Consignor of the Year
Lawrence Knapp won the Cosigner of the Year award at this year's CAR Conference.
Read More →
2026 CAR Awards Celebrate Industry Excellence
CAR’s annual Fleet Remarketing Awards opened a reimagined 2026 conference designed to bridge the worlds of fleet management and automotive remarketing.
Read More →
Inside the CAR2026 Awards: Leaders, Legacy & What’s Next
Here's a look inside the awards ceremony at the CAR Conference, where industry leaders reflected on the growth, impact, and future of automotive remarketing.
Read More →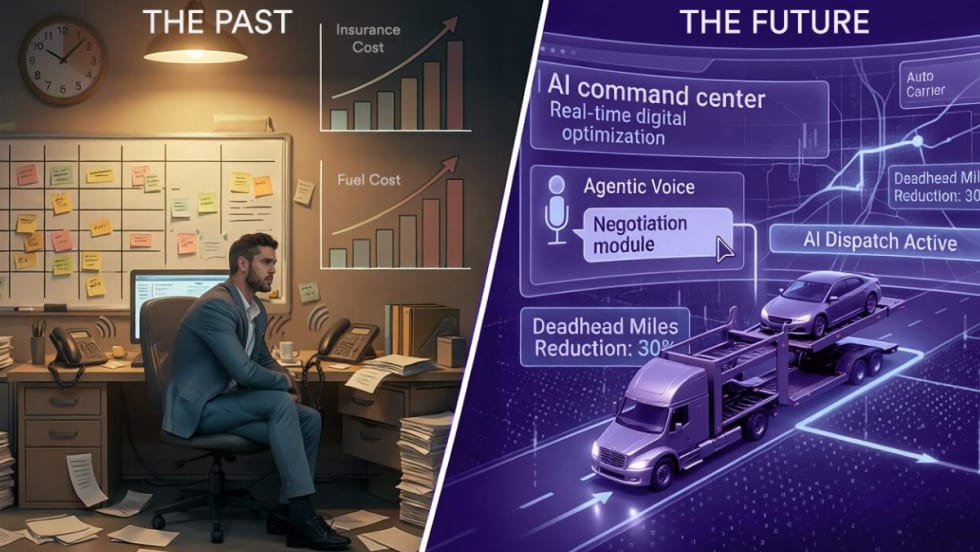
The Predictive Pivot: How AI and Data Are Redefining Auto Logistics in 2026
AI is no longer a luxury but the baseline for profitability in 2026. Auto haulers that adopt these tools now will quickly outpace those using manual workflows and taking a wait-and-see approach.
Read More →
The Predictive Pivot: How AI and Data Are Redefining Auto Logistics in 2026
AI is no longer a luxury but the baseline for profitability in 2026. Auto haulers that adopt these tools now will quickly outpace those that use manual workflows or take a wait-and-see approach.
Read More →